 Picking a digital signature vendor is an important decision. The product needs to be easy to use, and it also needs to produce documents that will be legally valid for the life of the document with no reliance on a third party. It can be confusing to find out if a vendor meets your needs, but never fear. We’ve come up with a handy checklist of eight things you should look for in a digital signature vendor.
Picking a digital signature vendor is an important decision. The product needs to be easy to use, and it also needs to produce documents that will be legally valid for the life of the document with no reliance on a third party. It can be confusing to find out if a vendor meets your needs, but never fear. We’ve come up with a handy checklist of eight things you should look for in a digital signature vendor.
1. Identity Authentication SIGNers must prove they are who they say they are by providing, validating or accessing some type of shared information.
- Does the digital signature service require users to prove their identity before applying a digital signature to a document?
- How strong is the authentication method? Does the system require that a user only receive an email, or does it require them to answer private questions or enter a code delivered to their mobile device?
- Can documents be accessed without authentication after being signed?
2. Audit Trail A feature that tracks EVERY action of THE signers and documents in each transaction to provide COMPREHENSIVE evidence of the entire transaction taking place.
- Does the signature solution track every event in the signature process?
- How detailed are the events being stored? What information is kept?
- How is the audit trail stored? Is it secured against tampering?
3. Notice and Consent ESIGN and other laws require that users know they are engaging in an DIGITAL signature process and must be able to opt out.
- Is the user presented with an appropriate and visible notice about using digital signatures?
- Is the user given an opportunity to decline to use the service?
- Is the consent to use e-signatures presented clearly?
- Is the user's consent tracked as an auditable action?
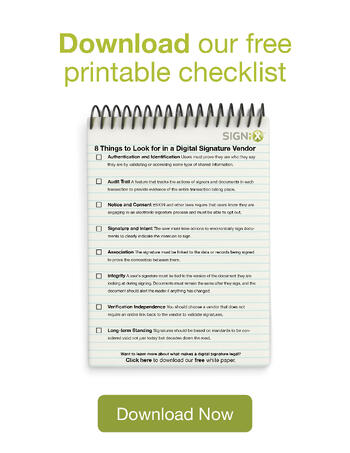
4. Signature and Intent The user must take an action to DIGITALLY sign documents to clearly indicate the intention to sign.
- How is the user prompted to sign a document?
- Does the process clearly communicate intent?
- How is the document viewed by a user? Is it the same as the final signed or printed version?
5. Association The signature must be linked to the data or records being signed to prove the connection between them.
- How is the digital signature linked to the documents being signed?
- Does the association of the signature rely on standards or proprietary solutions?
- Is the digital signature permanently embedded in the document or simply an image attached to it?
6. Integrity A user’s signature must be tied to the version of the document they are looking at during signing, and documents must remain the same after they sign.
- How are documents protected during the process of applying every signature?
- Does the service provide strong tamper evidence for the documents after they are signed?
- Can the service protect and also prove the integrity of a document at any point from the first signature to the last?
7. Verification Independence You should choose a vendor that does not require an ongoing contract to validate signatures.
- What format are the signatures and documents produced in? Is it proprietary?
- Are documents and signatures human-readable and also accessible using free PDF viewing software?
- Is each digital signature a permanent part of the document? Do the signatures inherently provide integrity to the document?
- Can individual signatures be validated without having to go back to the vendor that produced them?
- Do the signatures comply with international cryptographic and document standards, such as RSA, DSA, SHA, PAdES and PDF?
8. Long-term standing Signatures should be based on standards to be proven as valid not just today but decades down the road.
- Can the electronic signatures be validated long term?
- Does the digital signature service use technology that is based on standards and can be validated into the future?
- Are the systems used for signing proprietary to the vendor or based on established cryptographic tools?
%20formatted-1.png?width=2528&height=739&name=SIGNiX%20Logo%20Main%20(white)%20formatted-1.png)
