We're not calling you dummies, we promise. But all of this technology mumbo jumbo can be confusing, right? Here's our easy guide to digital signature technology. Electronic signature expert and SIGNiX director of product management, John Harris, joins us today to help break down the ins and outs of digital signature technology. Take it away John!
Electronic signatures. E-signatures. Digital signatures. These terms get tossed around a lot in the electronic signature industry and are often used interchangeably. But if you’ve spent much time on the SIGNiX website, you’ll know that we take these terms very seriously. We use digital signatures. We feel our customers deserve the best technology available to make their signed documents trustworthy and verifiable.
But trying to explain the technology behind digital signatures can be much more challenging. You see, they’re based on mathematical algorithms and advanced cryptographic concepts… a bit more complicated to explain than a pen and ink signature! At SIGNiX, we strive to make digital signatures as simple as opening the Internet, typing in a password, reviewing a document, and clicking the "sign" button. But behind the scenes, our service is busy dealing with all of this complexity because it delivers real value to our customers and their critical documents.
In this post, we’re going to decipher the mysterious world of digital signatures to help you understand why we use this technology and where it came from. Hang on, it might be a bumpy ride!
Defining the Benefits
First, let’s start with a definition:
A digital signature is a mathematical scheme for demonstrating the authenticity of a digital document. A valid digital signature gives the recipient reason to believe that the message was created by a known sender in a way that they cannot deny sending it (authentication and non-repudiation) and that the message was not altered in transit (integrity).
True digital signatures have very specific benefits:
- Authentication: SIGNiX provides various ways to identify a signer (from email verification to a text message to so-called knowledge-based authentication) so those persons can’t later say they didn’t sign the document.
- Non-repudiation: SIGNiX walks users through a series of steps to sign a document and tracks all of those steps. Doing so eliminates the possibility of a signer suggesting they made a mistake in signing or never ‘clicked’ a button.
- Integrity: Documents signed with SIGNiX alert the reader in real-time if anything has been changed or if there’s any reason not to trust the document. Freely available PDF viewers provide this functionality on- of off-line.
A digital signature on a document can look like this:
 |
Or it might look like this... |  |
That’s what a digital signature provides in practice. But what about that "mathematical scheme?" How does that technology behind the scenes create such rich benefits? To understand this better, we need to step back a bit in history.
 To the Time Machine
To the Time Machine
For thousands of years, civilizations have needed to send and receive secret messages. These secrets usually relied on codes that only the sender and the recipient knew. As long as the sender and receiver kept their knowledge of that code away from others, it would be very difficult to decipher the message in transit.
One example of this ‘shared secret’ method was the scytale, first described in ancient Greek texts. A specific length and thickness of rod would be created, and leather or parchment wrapped around it. The sender inscribed his message on the material, unwrapped it and sent it via a courier. After delivery, the receiver would wrap the length of parchment around a scytale of the same thickness and size to decipher the message.
This type of encryption is also known as a ‘symmetric-key’ system, where both parties use the same key to unlock an encrypted message. This methodology has remained essential to the practice of cryptography even to this day.

However, there is a challenge to this form of cryptography. A shared secret implies that you share the key with another person in order for them to decipher the message. How do you get that key to them securely?
Making Keys Public and Private
It wasn’t until the mid-1970s that two clever cryptologists named Diffie and Hellman speculated it might be possible to create a system where the sender had a pair of keys: one public, one private. Both keys were mathematically associated with each other so they could be used to encrypt messages, but in such a fashion that the public key could be shared freely without endangering the private key. The private key would remain protected by its owner.
Other scientists (Rivest, Shamir and Adelman (e.g. RSA)) worked on this idea too and collaborated to create the algorithms and standards at the heart of what’s now known as public key cryptography.
Let’s try to explain in simple terms how this new model works.
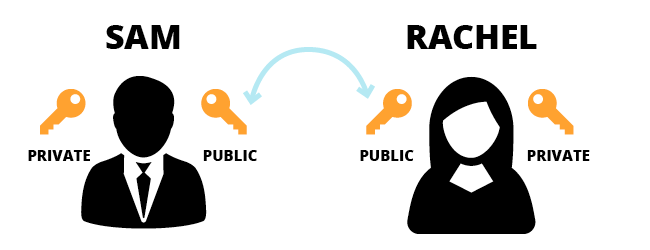
The sender, Sam, has a message he wants to send to Rachel. Instead of having to find a way to get a key to Rachel, both Sam and Rachel are using public-key cryptography. They both have a public and private key, and they’ve shared their public keys with one another.
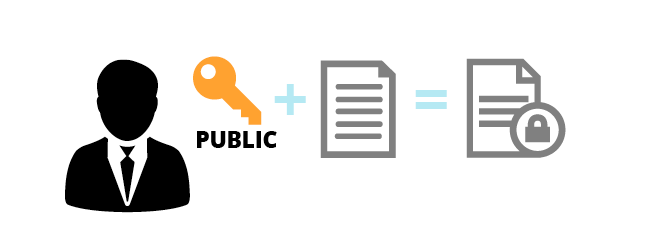
Sam uses Rachel’s public key to encode the message and then sends the encrypted message to Rachel.
Rachel uses her private key to decode (decrypt) the message and read it. Since only she had access to her own private key, no one else could decipher the message. Rachel could reply to the message and encrypt it, in turn, with Sam’s public key before sending it back. Sam would need his private key to unlock the reply.

Encryption is used to keep messages confidential, but what if you want to let people find out if a message was changed or explain precisely who it came from?
The Digital Signature Rises
Diffie, Hellman and others recognized that public key cryptography could not only encrypt messages but also answer these challenges. Since each user in this system possesses a unique key pair, including a private key under their own control, the system could be used to protect the integrity of an individual message and attest that a specific user sent it. In other words, a digital signature.
Let’s see how this works. In this example, Sam and Rachel are still sending messages to each other, but this time Sam not only wants to send a message to Rachel but also wants her to know that it came from him and that it didn’t change after he sent it.
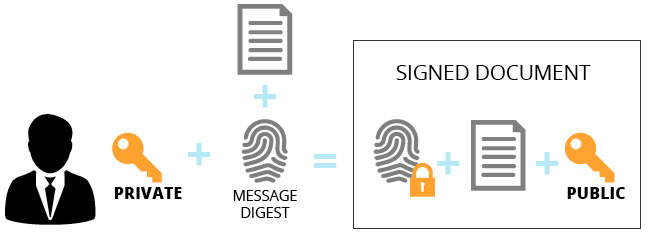
Sam creates his message and also creates a ‘fingerprint’ or digest of the message. He then encrypts this digest with his private key.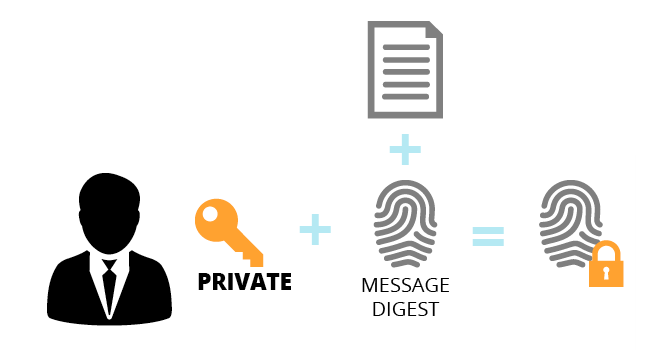
Sam then bundles the message, the encrypted fingerprint, and his public key together. This becomes the signed document, which Sam sends to Rachel.
Rachel receives the message and reads it, but wants to be sure it came from Sam unchanged. First, she creates a fingerprint of the message she just read. Then, she takes the encrypted message digest and decodes it using Sam’s public key, which was attached to the message as well.
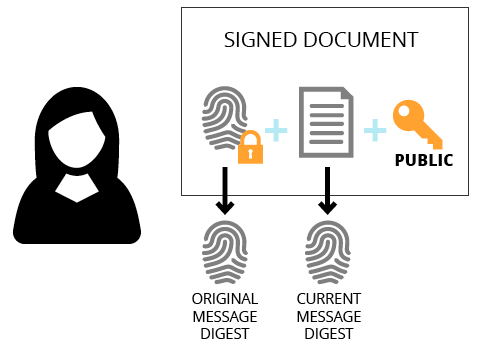 At this point, Rachel compares the two fingerprints. If they match, the message (1) came from Sam and (2) has not been tampered with. If it doesn’t match, then the message cannot be trusted.
At this point, Rachel compares the two fingerprints. If they match, the message (1) came from Sam and (2) has not been tampered with. If it doesn’t match, then the message cannot be trusted.
Bringing Digital Signatures Down to Earth
SIGNiX protects your private keys and authenticates you as a signer to provide you sole control over your signature (‘private key’) and also provide assurances to others that you are who you say you are. Our service creates the ‘fingerprint’ of your uploaded documents and applies digital signatures using the complex standards and algorithms published and created over the past three decades.
Recipients of your signed documents know they haven’t been tampered with since they were first signed. SIGNiX does this for every signer, every signature, and every document that goes through our system. You don't have to worry about checking whether the document has been tampered with. We do all of the work for you.
Want to learn more? Download our free ebook about digital signature security!
%20formatted-1.png?width=2528&height=739&name=SIGNiX%20Logo%20Main%20(white)%20formatted-1.png)