A digital signature is only as good as the security that protects it. After all, what good is a contract if someone can easily change the terms after it’s been signed?
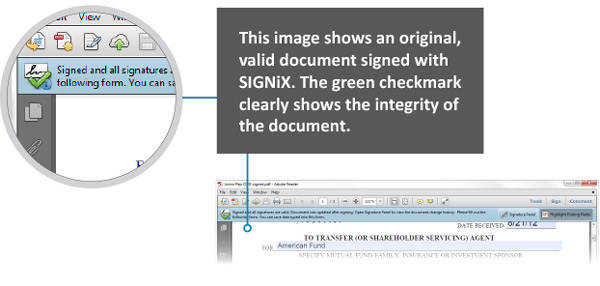
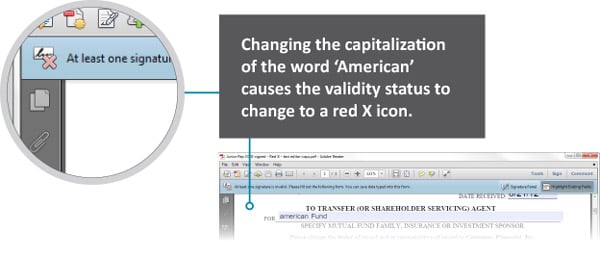
 That’s why many digital signature services offer a feature called “tamper evidence.” If someone tries to change any part of the document (even something as simple as deleting a space or capitalizing a word), there’s proof that changes took place.
That’s why many digital signature services offer a feature called “tamper evidence.” If someone tries to change any part of the document (even something as simple as deleting a space or capitalizing a word), there’s proof that changes took place.
With SIGNiX’s digital signatures, documents are tamper-evident not just at the end of the signing process, but from the moment the transaction is created because each signature and initial includes a tamper-evident seal at the time of signing. This provides evidence that the first signer didn’t alter the document before it was sent to the second signer. Pretty neat, right?
If you’re dealing with important documents or high-value transactions, advanced tamper evidence is vital. In fact, many banks, credit unions and financial advisors require this kind of tamper evidence to protect their customers.
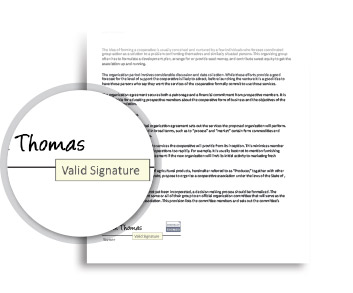
Instant Feedback Inside Each Document
SIGNiX-signed documents can be easily verified using free PDF reader software. There’s no need for you to be online. All you have to do is hover over a signature to find out if the signature is valid. To see more information, simply click on the signature to open the Signature Properties dialog box.

This dialog box contains a rich set of information about the signature: the name of the signer, a timestamp of the signature, the nature of the document when it was signed and other technical details.
This is a quick and easy way to know if your documents have been tampered with. SIGNiX’s documents also come with a highly detailed audit trail.
SIGNiX’s digital signatures offer you verification offline and are embedded into the document.
Contrast that with most other electronic signature vendors. Instead of including the data you need to prove the document is valid within the document itself, they send customers back to the vendor’s own website to retrieve information about the signature.
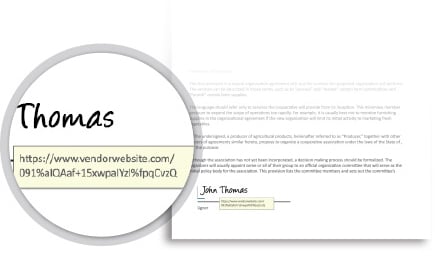
The signature isn’t embedded into the document—in fact, information about the signature is likely stored with the vendor.
And even though the vendor may let a customer download these documents, if there’s ever a question about an individual’s signature, the lack of information in their audit trails means the customer must always come back to the vendor, resulting in vendor lock-in.
The image below shows the link presented when you hover over a signature created by another vendor. Clicking on it opens a browser window, requiring that a recipient be online to get at any additional information.
Worse, if the vendor’s website goes down or the vendor goes out of business, you wouldn’t have any evidence to prove that your documents are valid.
In addition to this verification, PDF reader software also includes an automated way to alert you if any tampering has happened to your documents.
Secure Tamper Evidence in Action
With SIGNiX-signed documents, any change in a document will trigger the PDF viewer to notify you of the change, in real-time. The signatures are embedded directly into the PDF and are available at any time, offline or online.
These layers of tamper evidence aren’t always present in other e-signature solutions. Some don’t even render their e-signed documents tamper evident, as we showed previously, making it possible for fraudsters to take a signed document, change the terms and try to pass off the altered version as the original.
Other e-signature vendors often use a different signature technology to tamper seal a document than is used to sign the document. Moreover, they apply this seal only after each party has signed. Not only does this make it difficult to know if a document was altered in-transit, it can also produce inconsistencies in evidence.
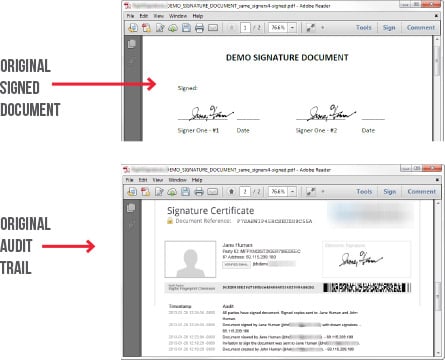
Ineffective Tamper Evidence
Compare that level of tamper evidence to other e-signature vendors. In these screenshots, a document has been signed twice by a single person using another e-signature vendor’s service. The first screen shows the signatures, but since there’s no tamper-evidence applied to the document, there are no green checkmarks or any security feature or control on the document itself.
The second image contains all manner of seemingly secure elements including bar codes, ‘checksums,’ and a high-level audit trail, and thus seems to be protected from changes—but not everything is what it seems.
What happens to the document after a line of text is added to the PDF using tools provided by the PDF viewer itself? The images below show the results. Other than the additional line of text, there is no real-time indication that the document has changed considerably. Everything else remains exactly the same.
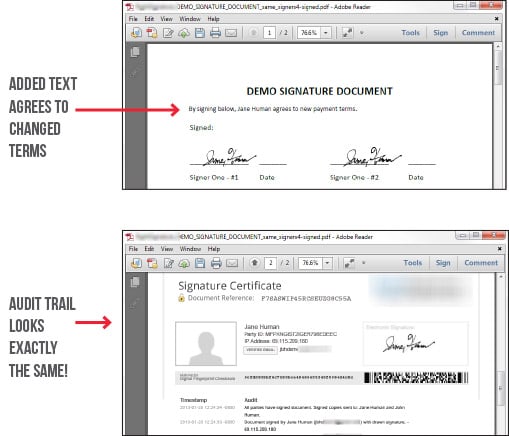
The security features touted by this vendor require the document recipient to take an active role in verifying the document. There is no information stored within the document to show a change was made—that information must be requested from the vendor, which assumes the vendor is still in business and won’t charge you to access this information.
True digital signatures (like the kind used by SIGNiX) are not only easier to verify than documents signed by other vendors, but they're also infinitely more accurate. That's why we're trusted by some of the most highly regulated organizations in the country—financial advisors, banks, credit unions and hospitals.
To learn more about document security, download our free eBook to find out the 8 rules for e-signature security.
%20formatted-1.png?width=2528&height=739&name=SIGNiX%20Logo%20Main%20(white)%20formatted-1.png)